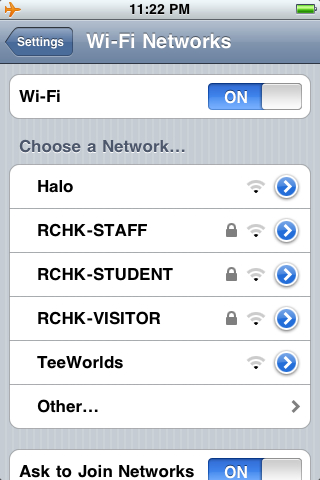
The Hong Kong International School has setup what I consider to be a “best practice” wifi network. Like many universities, the school has segmented its wireless network into different virtual LANS (VLANS) to cordon off access for different groups. One wireless network is available for faculty and staff, another for students, and a third for guest users.
FYI, I wasn’t viewing the HKIS network after 11 pm last night – my iPhone is still showing mountain time since I’ve left it on “airplane mode” since flying to Asia for the week. 🙂
Our schools need to be preparing NOW for students to bring their own wireless devices, including laptops and wifi-capable smartphones, to school. Several of the international schools here in Hong Kong are doing just that. While the cost of 1:1 computing initiatives is coming down thanks to the advent of netbooks, many schools will be able to afford to permit students to bring their own computing devices to school before they will be prepared to fund a student laptop initiative. To prepare the networking infrastructure to support this “BYOL” (bring your own laptop) environment for students, K-12 school networks need to grow to resemble university networks. Intrusion protection systems can port-scan new computers which ask for a wifi IP address on one of the segmented school network VLANs, and as long as that computer is not infected with malware it can be granted access to both the VLAN resources as well as the commodity Internet. Bandwidth can be allocated / throttled as desired between the VLANs, so particular users (like students or guests) do not “hog” the network resources.
Some educational IT leaders and staff members are sure to balk at this proposal. Of course this will mean more work and a “messier” computing environment than one which is more tightly controlled and centrally managed. Internet platform access options are proliferating, however, and the world is NOT going to standardize on a single operating system or access device. We need to prepare our school networks to safely and securely permit student and visitor access, and creating separate VLANs to cordon off access for different types of users is a step in the right direction.
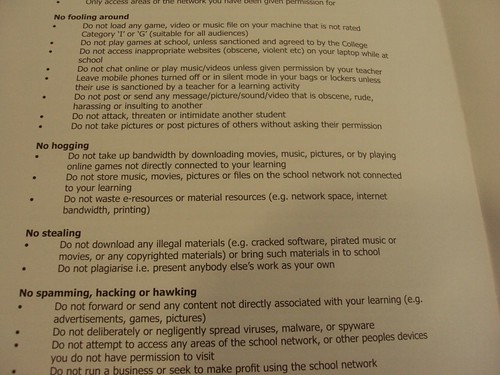
The acceptable use policy (AUP) for Discovery College in Hong Kong was collaboratively created by students, parents and teachers. It uses plain language that is clear and to the point, and addresses the issue of bandwidth abuse. The AUP delcares, in addition to “no fooling around,” that there will be “no hogging” of bandwidth on the network. Hear, hear!
Technorati Tags:
1:1, 1to1, laptop, network, networking, security, wifi, vlan, segment, byol
If you enjoyed this post and found it useful, subscribe to Wes’ free newsletter. Check out Wes’ video tutorial library, “Playing with Media.” Information about more ways to learn with Dr. Wesley Fryer are available on wesfryer.com/after.
On this day..
- Beyond the Bake Sale: Building Social Capital in our Schools by Dean Shareski – 2013
- AT&T Unlocked My iPhone4 Today – 2012
- Streamlining Blog Post Submissions with TDO Forms on WordPress – 2011
- Visual Literacy, Talking with Images and Curiosity Amplifiers – 2011
- Educational TED Talks at #learning2cn – 2010
- Education 3.0: A Framework for Change in Teaching and Assessing 21st Century Skill by Andrew Thomson – 2009
- School Administrator Questions about 21 Century Learning – 2009
- Our 21st Century Challenge: Developing Responsible, Ethical and Resilient Digital Citizens by Robyn Treyvaud – 2009
- Brisingr plot speculations – 2008
- Ways to use a wiki – 2008

Comments
3 responses to “Best Practice WiFi Networks in Schools”
Wes, any chance you can post the full AUP? That may be a good model to use in our schools.
Interestingly, I wrote about this topic and the process happening in the state of New South Wales, Australia relating to implementing 1:1 computing and universal wireless access within a school. Take a look: http://paralleldivergence.com/2009/08/20/is-this-technically-the-best-11-rollout-in-the-world/
Reading through your spec, I can’t see free-roaming happening. If students move from one part of the school to another, will the client know to let go of one WAP to connect via another? How do the WAPs handle load balancing? if there are two WAPS in the general vicinity, how does one WAP know when it’s “full”?
The NSW system is one solution for all users. 802.11N-only, authentication via AD/Radius, Rogue WAPs can be discovered and killed. It’s very impressive.
I will try and do that, Richard. You might see if it is included in the parent handbook link below. I can’t see the flash plugin since I am on my iPhone to check, but my photo was of the AUP in the Parent Handbook:
http://www.discovery.edu.hk/cms/index.php/en/information/parenthandbook