The growing ubiquity of technology in our lives has made many parents into accidental home IT managers. How many different laptop, desktop, tablet, and mobile phone computers do the people in your household now operate and use? Another way to ask this question is: How many different devices in your home connect to the Internet via a wifi or an ethernet cable connection? Whatever that number is, that is the number of separate devices which need to be updated REGULARLY so security patches are installed that address identified security vulnerabilities. The problem is, many adults and kids don’t realize how critical this REGULAR software updating process is. When combined with ignorance/naivety about online phishing schemes, this can become a recipe for identify theft and “sextortion plots” when malicious hackers gain remote control of computer webcams. RAT (Remote Administration Tool) hacker software is rampantly and freely available online, and the most malicious/harmful variants are WindowsOS only. These online threats provide more reasons to ditch / replace your Windows-based PCs FOREVER with better and more secure alternatives which provide a smaller “target market” for hackers. That means running MacOS/iOS or Chromebook computers. According to the Electronic Frontier Foundation (EFF):
Currently, running a minority operating system significantly diminishes the risk of infection because fewer malware applications have been targeted at these platforms. (The overwhelming majority of existing malware targets only a single particular operating system.)
In our family our number of home wifi devices is an astonishing 17. If we add the personal iOS devices my wife uses with her students in her classroom at school, that number grows to 22. Fortunately, none of those devices are Windows-based PCs, or run a variant of the Windows operating system. (WinXP, Win Vista, Win7, Win8, etc.) As an elementary classroom teacher in Lubbock, Texas, I wrote and published the article “Wagging the Dog in Educational Technology: Elevating ‘IT’ Into the Classroom” in January 1999. The article documented the ways computer lab teachers using Windows95 and Windows98 were forced to learn and follow ridiculously complex steps to get computers to do basic things like connect to the Internet and the local network, when compared to the steps required on Apple/Macintosh computers. The most immediate result of that article was a disciplinary meeting in the office of my superintendent, with my principal, who firmly told me never to publicly write anything that would bring discredit upon or otherwise make our school system “look bad.” (He also pledged privately to my principal that I would never be promoted as a teacher to a higher position within our school district since I had written that article.) Long term, however, writing that article and becoming intimately familiar with the differences in not only using but also supporting Windows-based PCs compared to Apple/Macintosh computers led me to become an even more fervent user, supporter, and volunteer-evangelist for Apple computers. I have learned to express my love for Apple technology, and now Google technology tools, with the following statement:
I love simple, powerful tools that just work – and don’t have any malware or virus problems I have to worry about.
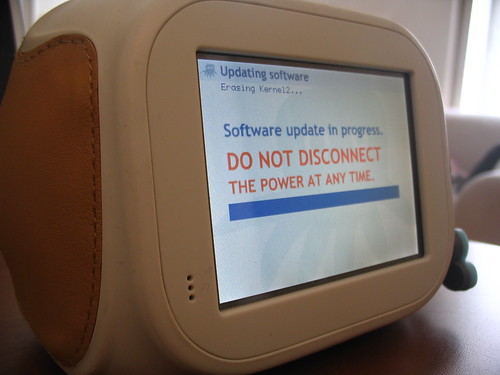
Updating the software on computing devices is EXTREMELY important, because new security vulnerabilities are constantly identified for ALL platforms. Malicious hackers (including “script kiddies“) exploit those vulnerabilities for harmful and nefarious purposes. If you, members of your family, and the students you teach in class are not already familiar with the terms Botnet and computer zombie, spend some time reading those respective WikiPedia articles and then discuss them. This isn’t science fiction, it’s real, and it’s the way hackers gain access to personal bank accounts and more (including WindowsOS-based webcams) on the computers people use every day.
According to the EFF’s “Malware” page on their Surveillance Self-Defense site:
Malware is a catch-all term refering to software that runs on a computer and operates against the interests of the computer’s owner. Computer viruses, worms, trojan horses, “spyware”, rootkits and key loggers are often cited as subcategories of malware. Note that some programs may belong to more than one of those categories.
Using a non-Windows-based PC or mobile computing device does NOT guarantee you won’t ever be affected by malware, but it’s huge step forward in the quest to keep you and your family safe from nefarious hackers. Again according to the EFF:
Nobody knows how many computers are infected with malware, but informed estimates range from 40% to almost 90% of computers running Windows operating systems. Infection rates are lower for MacOS and Linux systems, but this is not necessarily because Windows is an easier target. Indeed, recent versions of Windows are much improved in security. Rather, more malware authors target Windows machines because an effective attack will give them control of more computers.
Why are so many computers compromised, and part of wide-ranging botnets used for DDS attacks and cyber-espionage worldwide? Two of the biggest reasons are:
- A large number of people and organizations worldwide still run the most vulnerable computer operating systems in the world: Variants of the Windows OS (especially older versions)
- Many individuals, especially home users, do not regularly update the software on their desktop computers, laptops, tablets and mobile phones.
Fortunately, updating mobile device software has become MUCH easier, thanks to Apple’s App Store model. Lots of people gripe about iTunes, but the app store model represents a HUGE leap forward for computing from a security standpoint. Simply open the App Store on your device, click Updates, and click Update All. Put in your password and wait… that’s it. The success of this model in streamlining the software updating process for users has caused Apple to create an App store for its line of laptop and desktop computers too. This is a GREAT thing from a security standpoint.
Two years ago at the Google Geo-Teacher’s Institute in Lewiston, Maine, I had my first opportunity to use a Chromebook. The following phrase (referencing the 1996 Tom Cruise movie, “Jerry Maguire“) summarizes my reaction:
You had me at 8 seconds.
8 seconds is the startup/boot-up time for a Chromebook. In addition, the Chromebook does not have any locally installed software programs, everything runs off the web. From a system administrator’s standpoint (or a parent at home needing to update software on different family member computers) it’s a dream come true.
So why is this post titled, “RATs, WebCams & Online Predators?” The reason is Nate Anderson‘s article for ARStechnica yesterday, “Webcam spying goes mainstream as Miss Teen USA describes hack.” You NEED to read this entire article and discuss it with your spouse / significant other, children/grandchildren (depending on age, of course) and students. With younger students, I wouldn’t go into all the details, but the idea that it is now COMMON for malicious hackers to gain control of Windows-based computer webcams is scary and bad. The opening paragraph of the article summarizes the problem and situation:
Webcam hacking has officially gone mainstream with yesterday’s revelation that the new Miss Teen USA, Cassidy Wolf, was the victim of a “sextortion” plot in which someone slipped Remote Administration Tool (RAT) software onto her computer and used it to snap (apparently nude) pictures of Wolf in her room. “I wasn’t aware that somebody was watching me (on my webcam),” she told The Today Show. “The light (on the camera) didn’t even go on, so I had no idea.”
Yesterday’s CBSnews.com article, “Cassidy Wolf Update: FBI investigating Miss Teen USA’s claim she was a victim of cybercrime “sextortion”, reveals a perpetrator has been identified and this single individual may have over 12 different female victims.
To get more background on this crazy to believe situation, which could be affecting your family right now if you’re still using and running Windows-based PCs, read Nate Anderson’s March 2013 article, “Meet the men who spy on women through their webcams: The Remote Administration Tool is the revolver of the Internet’s Wild West.” Beware the article starts with profanity, so you won’t want to bring this up on your classroom projector for students. On page two Anderson wrote:
Today, a cottage industry exists to build sophisticated RAT tools with names like DarkComet and BlackShades and to install and administer them on dozens or even hundreds of remote computers. When anti-malware vendors began to detect and clean these programs from infected computers, the RAT community built “crypters” to disguise the target code further. Today, serious ratters seek software that is currently “FUD”—fully undetectable.
Using a Mac computer, iOS mobile device, or Chromebook does NOT offer a 100 percent guarantee an individual or organization will avoid all instances of hacking, phishing or malware. These situations are not only about the computer hardware and software people use, they are also about the CHOICES people make using them. Given the fact that Windows-based systems are THE #1 TARGET worldwide of malicious hackers, however, it’s a no-brainer for me that WindowsOS is the operating system to avoid today at all costs: At home, at school, and in business. You may not be able to change the operating system of choice where you work or study this month, but you CAN change it at your house. The “Friends Don’t Let Friends Use Internet Explorer” campaign needs to expand: Friends shouldn’t let friends use Windows-based computer systems either.
At the end of Nate Anderson’s March 2013 article, “Meet the men who spy on women through their webcams,” he provides advice for people who will continue using Windows-based systems vulnerable to RAT software and human predators:
RATs aren’t going away, despite the occasional intervention of the authorities. Too many exist, plenty of them are entirely legal, and source code is in the wild (a version of the Blackshades source leaked in 2010). Those who don’t want to end up being toyed with in a YouTube video are advised to take the same precautions that apply to most malware: use a solid anti-malware program, keep your operating system updated, and make sure plugins (especially Flash and Java) aren’t out of date. Don’t visit dodgy forums or buy dodgy items, don’t click dodgy attachments in e-mail, and don’t download dodgy torrents. Such steps won’t stop every attack, but they will foil many casual users looking to add a few more slaves to their collections.
We need to be discussing Internet safety and digital citizenship not only with students at school, but also with our family members at home. Is a grandparent in your family using a Windows-based computer? If so, chances are VERY high that computer is infected with malware and may be part of a global botnet used for online extortion schemes and/or cyber-terror attacks. Sound too fanciful to believe? Follow the links I’ve provided in this post and read for yourself. Also see my May 2005 post, “Lucrative high tech crime” and May 2006 post, “Lawlessness and extortion on the cyberfrontier” for more background.
I am NOT a fan of consistently or exclusively using fear as a motivator to change behavior. That’s been the central focus of U.S. educational policy as well as U.S. foreign policy for many years now, and I’m sick that approach in both domains. I am also not a naive idealist when it comes to life and human nature, however, and as both a parent and an educator it’s vital I’m well informed and proactive when it comes to protecting my family and my kids.
Our family ditched Windows-based PCs years ago. Perhaps it’s time yours did too.
Technorati Tags: technology, rats, rat, computer, malware, virus, safety, digital, citizenship, cassidy, wolf
If you enjoyed this post and found it useful, subscribe to Wes’ free newsletter. Check out Wes’ video tutorial library, “Playing with Media.” Information about more ways to learn with Dr. Wesley Fryer are available on wesfryer.com/after.
On this day..
- Radio Spot for iPad With Wes Workshop in Oklahoma City: Friday, September 14th – 2012
- Ways to Subscribe to a Blog in Google Reader on an iPhone, iPad or iPod Touch – 2011
- Watch Flash Videos & Play Flash Games on iOS Devices – 2011
- Multiple Choice Testing on an iPod Touch with NearPod – 2011
- Do You Realize? (21st Century Education in New Brunswick, Canada) – 2010
- A gaggle of AudioBoos from the Oklahoma City Zoo – 2009
- MNet Social Safety Resources – 2008
- Download offline copy of a VoiceThread digital story? – 2007
- Fun with 43 places, 43 things – 2005
- 5 conversations about podcasting – 2005






Comments
7 responses to “RATs, WebCams & Online Predators: More Reasons to Ditch Windows-based PCs Forever”
So I guess all those years that schools spent saying “Kids need to learn Windows and Office” bacause that is what businesses use was basically wasted time…
Oh no, I wouldn’t say so. Viable digital literacy skills are transferrable, so things we learn to do on a Windows computer inform what we do on a Mac, Chromebook or Linux-based computer. The idea that “businesses use Windows and MS Office therefore we should be doing Excel spreadsheets in kindergarten” has always been a silly idea, however. 🙂
The problem with this kind of thinking is that when everyone switches to a Mac OS, so will the hackers. They don’t target Windows users because it’s easier, they target them because they’re the largest user base. I’d also add that almost every Mac computer comes with a built in web cam whereas most Windows desktop users probably aren’t buying an external web cam.
It would be better to advise people to maintain their security software and maybe through a towel over their web cam when they’re not using it.
[…] http://www.speedofcreativity.org/2013/08/17/rats-webcams-online-predators-more-reasons-to-ditch-wind… […]
Why on earth would you honestly give people that advice? Windows IS the #1 hacker target. That may change, but it hasn’t yet. Why should people stick with Windows? Unless you have to use/run a program that isn’t available on a Mac or Linux system, I see no compelling reason what-so-ever to run a Windows computer today given this context of hacking. Why would you advise people to stick with Windows?
I wouldn’t advise them to choose one over the other at all. You use what works best for you and your budget (not everyone can afford a Mac). The idea that a Mac is somehow hackerproof is misguided. Mac users don’t deal with security problems as much as Windows users because they represent a small sampling of computer users. If everyone switched to Macs, then Mac users would become the number one target of hackers.
It would be far better in the long run if people learned how to be responsible with their technology than to rely on the brand of their computer to keep their information safe.
I definitely agree everyone should learn to responsibly use whatever technology they have, laptop, smartphone, tablet, etc. What you describe could come to pass: If a large enough majority of people ditch Windows and move to Apple’s OS, it would become a bigger target for hackers and this comparative benefit in terms of security would go away. The point is: That is NOT happening, so people DO have the opportunity (in the words of the EFF) to use “a minority operating system.” That also includes Linux, but most people don’t want to be as geeky as running Linux sometimes requires.
In terms of cost, just look to the used market. We have a great store in OKC, CD-R Electronics, that sells basically every kind of used Mac from the last 4 years (laptop and iMac) at a fraction of new prices. http://cdrokc.com I was there two weeks ago and they had several 3rd Gen 11″ MacBook Air laptps for $500, as an example. Laptops and desktops have gotten so fast in the past few years that a used computer can still be lightning-fast / more than adequate for most user’s needs.
The hassle of having to run anti-virus software is something I don’t have to bother with as an Apple laptop user. Certainly I COULD run antivirus, but there aren’t any malware programs “in the wild” for Macs that are infecting machines – and there are thousands upon thousands for Windows. I’m guessing based on your responses that you haven’t tried using a Mac exclusively for a few weeks, in the past few years? I’ve done that with Windows systems, and I help out a fair number of folks who use Windows machines, so I have firsthand experience with the difference. It’s incredible.
Many Windows users don’t realize they don’t have a choice and don’t have to put up with the horrifically hostile security environment which is the Windows OS today. “Normal” is defined relatively, and many people fear the changes which would be required if they try something new. That’s unfortunate but human nature. On the security side, that would seem to weigh in favor of the MacOS not becoming dominant in the next few years and replacing Windows as the #1 hacker target. All the more reason to switch to Apple. 🙂