This may be the most important post you’ll read on my blog from a personal, digital security standpoint. If you use ANY website today which requires a login but does NOT use a “persistent https” secure connection thereafter, you’re at MAJOR risk of having your account(s) hacked if you use open, wifi hotspots in coffee shops or other locations. Yes, this means Facebook, at least for now until they FINALLY deploy persistent https. This danger is real, this is not a “Chicken Little” story, and in this post I’ll explain why. The bottom line for me is, I’m now using a commercial VPN service (Astrill) whenever I’m connecting my laptop on any type of network (a wired hotel connection or a public wifi connection) other than one I own at my house, or via my 3G AT&T network connection. I want to thank James Deaton (@jed on Twitter) for alerting me to this risk demonstration (Firesheep) at OpenBeta5 last week in Oklahoma City.
For a more in-depth, geeker explanation of the problem which Firesheep exploits and dramatically demonstrates, read Glenn Fleishman’s October 28, 2010, article for BoingBoing, “Liar, Liar, Sheep on Fire.” I’ll begin with a visual illustration. After installing the free FireFox extension FireSheep this evening at a local coffee shop, I was immediately able to gain access to the Facebook accounts, WordPress blog administrative dashboards, and other SUPPOSEDLY private, secure profiles of the following web users on different sites:
I am not a hacker, I’d classify myself as a “medio picante” geek… So how did I do this? The reason is Firesheep: A simple, easily installed FireFox extension which allows ANYONE to gain this kind of access on a shared Internet connection…. Not just black hats, white hats, or script kiddies. MANY websites, including Facebook today, do NOT use a “persistent https” connection after users login. This means the browser address changes to “https” and creates a secure “tunnel” during the login process, but thereafter users’ browsers return to a “http” unsecure connection while a “browser cookie” is set to maintain the login. When using a common router, as users do in most coffee shops and other locations where open, unsecured wireless connectivity is provided, those browser cookies are essentially “shouted out loud” for anyone to read / hear / copy / use. Eric Butler, a freelance web application and software developer in Seattle, Washington, released FireSheep on October 24, 2010, at the Toorcon12 conference in San Diego as a free, open source plug-in for the FireFox browser to demonstrate this security vulnerability and its seriousness. Eric got my attention, and he should get yours too.
I’ve read and heard about the dangers of open wifi connections for years, but until seeing FireSheep in action myself, I wasn’t a believer. Now I am. When I was in Shanghai, China, in September 2010, I utilized Astrill to bypass the Chinese content filters and gain access to sites like Twitter, Diigo, Google Sites, and other web destinations I regularly use for my work as an educational consultant. I’ve read about how hackers (and even script kiddies) can use software programs like Ethereal and “Winsock Packet Editor” to view userids and passwords sent “in the clear” over http connections. I didn’t realize the process could be so easy and straightforward as Firesheep makes it, however. The release of Firesheep onto the world stage means something very important for all of us: We should NOT assume our Internet “sessions” (website logins) are secure or private when we are using most public / shared wifi or wired Internet connections.
Glenn Fleishman includes a variety of suggestions in his article on Firesheep for what “we” should do to protect ourselves from this acknowledged and pervasive web vulnerability. I’ll highlight a few of these.
SUGGESTION #1: AVOID LOGINS ON UNSECURE NETWORKS
His first suggestion is one we all should implement immediately: “Engage in no unsecured Web logins when working on an untrusted network, public or otherwise.” This means we should log OUT of all websites for which we’ve “saved our passwords” in all the web browsers we use or have open on our computers, when we’re on an unsecured network connection, and NOT login to them unless we use a VPN.
Translated into plainer language, this means: Don’t use Facebook EVER at a coffee shop, unless you’re taking geeky precautions. (Using a VPN.)
SUGGESTION #2: USE HTTPS EVERYWHERE WITH FIREFOX
HTTPS Everywhere is another free plugin for FireFox, but it’s designed to keep you more secure online. For websites which permit https / secure connections, the plugin FORCES the website to use those https “tunnels” so your web traffic stays secure and confidential. I prefer using the Google Chrome browser over FireFox in most cases, so this suggestion isn’t one that will help me a great deal. I have installed it on my FireFox browser, however, so it will be an option for me if I forget or don’t renew my VPN.
SUGGESTION #3: USE A VPN SERVICE
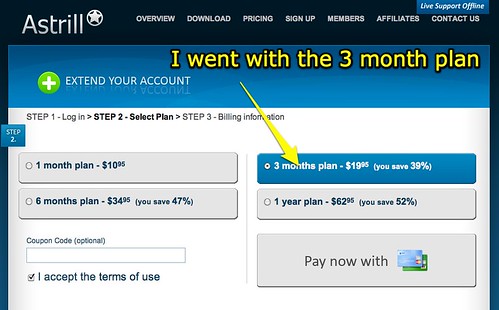
A VPN is a “virtual private network,” and VPN connections are used frequently by business travelers to connect back to their home / small business / corporate office to securely access web applications. At one time, people who wanted to use a VPN connection had to purchase and configure hardware to which they connected their laptop(s) when away from the office. Today, however, a variety of commercial options are available which provide VPN services on a monthly or annual basis. I had very good experiences with Astrill in September when I was in China, connecting via my laptop, iPhone, and iPad, so I decided to activate a three month plan with them today for $20. I figure I’ll give this a try, and if something better comes along I’ll switch in three months.
Astrill does NOT require users to download anything on an iPhone or iPad to use the service. Instead, you simply configure your VPN connection with the server address and login credentials for your account. On a laptop computer, however, Astrill provides a downloadable client application which you use to connect to the service when you want VPN tunneling.
CONCLUSIONS
I wrote the post “Wireless and hotel Internet security” back in December 2005, after listening to a Security Now podcast about hacking, packet sniffers and VPNs. I didn’t take the inconvenient steps at the time, or until today, of actually paying for and using a VPN connection on unsecured network connections. After seeing Firesheep in action before my eyes tonight, however, I’m a believer and am changing my web surfing ways on unsecured networks. I’d encourage you to do the same, and share this information with others.
Even though web services like GMail DO use persistent https connections, once you are logged into Google their “cookie” is set in your browser and allows other Google web services which do NOT (currently) use https to be accessed by others using methods like Firesheep. My best advice is: When you’re on an unsecured network, assume you’re being packet sniffed. It’s simply too easy for people to do it now, and the costs to your online digital footprint as well as relationships (face-to-face as well as virtual) could be very high if someone chooses to hack your cookies.
If you choose to give Astrill a try, please use this link which includes my “affiliate” code. It won’t make a difference in terms of your costs, but my account will receive some credit… and I’ll consider that a “thank you” for this very important security “heads up.” 🙂


Comments
10 responses to “Firesheep should get your ATTENTION: Open Public Wifi Dangers are REAL”
Great security update, Wes. Thanks for sharing. Like you, I’m a Chrome user. Are you aware of any extensions for Chrome that act in a similar fashion to HTTPS Everywhere for FireFox?
John: I’m not aware of a similar plugin for Chrome, yet. Since it’s not open I don’t think Chrome is as extensible as FireFox. The project FAQ indicates the developers don’t think they’ll be able to write it for Chrome. I think a VPN solution is the best bet for unsecured networking connections, which redirects all your web traffic through the VPN. That way you’re covered, whether the website supports https or not. This slows down your connections, but the added security makes it worthwhile.
Thanks for the heads up, Wes. Let me know where/when the next OpenBeta is.
I think it’s always this time of year (late Oct) and they’re held at the OKC CoCo. The website for the event is openbeta.extendedbeta.com.
This morning I installed Firesheep on my Mac and was able to capture a Facebook session I initiated from another computer on a wireless network that does use a password (although not encryption). It was far too easy and if nothing else I hope that the advent of this plugin raises industry awareness over the need for encryption as a standard versus the unencrypted standard that currently exists.
As it stands right now, only Firefox has the EFF’s HTTPS Everywhere plugin although I hope that Microsoft patches or modifies IE to support a similar operating standard. I’m not sure where Chrome plugins stand at this point.
Thanks for helping to raise awareness around this Wes! Hopefully our online community will take this and run with it!
A Chrome extension is Use HTTPS, found at: https://chrome.google.com/extensions/detail/kbkgnojednemejclpggpnhlhlhkmfidi which can be used to configure specific sites to always use HTTPS connections.
Great post, Mr. Fryer. You do a wonderful job of explaining how serious this security issue is and ennumerating ways one can protect himself.
This whole Firesheep exploit brings up a question for me. Should I have the same security concerns when using mobile platform APPS (e.g. Facebook for Android or Twitter for iPhone) instead of web browsers?
Makalani: If you are on a shared wifi network, the security issues raised in this post are relevant whether you’re online with a laptop, a handheld mobile device, or something else. The “cookie” which is set and maintains your authenticated connection to Facebook (and hundreds of other sites which don’t use a persistent https connection) are sent in the clear, and can be captured by Firesheep. So, as far as I know, the answer to your question is YES.
Very good post – I started an FB gGoup (Secure Online Browsing with Public WiFi) under my FB account to discuss this very issue and have already started alerting my FB friends about this……. The group is “open” and you are welcome to join.
One comment – you are entirely correct about the FB “non-persistent” nature of their HTTPS: connection. If you set FB to https:// properly and then use most any of the FB “Apps” – then FB forces the browser back to http://. It warns about this – but what FB does NOT tell the user is that FB changes your Security setting (permanently until changed again) – back to http:// !! This is very dangerous and not well understood. So just using an FB App (i.e. I like Bejeweled Blitz) – will modify your FB settings back to http:// (permanently until you manually change it again!!). I comment on this scenario and suggest usage of a VPN
service.
I will cross post your article with your permission to my FB Group
http://www.facebook.com/home.php?sk=group_112275135515702&ap=1
Thanks Regards – John (john4sd on Twitter, FB, …. )