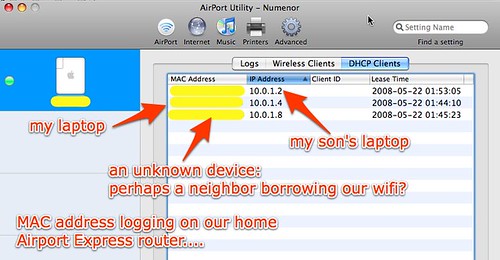
This evening after I removed wireless encryption from our home network to accommodate our new XO laptop, I started reviewing the wireless router logs on our Airport Express router and access point to see if any previously unknown or unwelcome visitors were attached to and using our wireless network. Using the Airport Utility application on my Macbook (which is also available for Windows computers, incidentally) I was surprised to see three devices attached to our wireless network with assigned IP addresses. We should have just had TWO devices attached: my laptop and my son’s. The following image shows the current DHCP leases for our router, which are set to expire after 4 hours. An entry can remain in this list after a device is turned off, but the middle tab on this menu shows the currently attached wireless clients (by MAC address only, not IP address as in this menu) and it also showed three currently connected devices:
Before I detail this situation further, I would like to address the reasonable question “Why should I care if my neighbors are on my wifi connection?” Most likely, if your neighbor accesses the Internet through your connection nothing bad is going to happen. HOWEVER, in the event that person chooses to do something illegal and their web activity is traced back to your home IP address, law enforcement officials could reasonably come knocking on your door. That was one of many messages shared by Larry Boggess of the Oklahoma State Bureau of Investigation (OSBI) last week at a workshop on Internet Safety hosted by the Oklahoma Library Association. Protecting yourself from being blamed for the illegal online activities of others is one big reason to have secure encryption on your home wifi connection. Another reason is to prevent a hacker attack: If someone is able to attach their computer to your home wifi network, they can use software to “sniff” all the packets passing through your router to and from the Internet, and even intercept your usernames and passwords for websites that do not use SSL encryption (passwords sent in the clear.) Identity theft is a real issue and a growing problem everywhere. According to Oklahoma policeman Kenneth Tidwell, there were over 17,000 cases of identity theft in Oklahoma alone last year and that number is growing fast. Companies like LifeLock are NOT emulating “Chicken Little:” Identity theft is a REAL problem that is only getting worse as more and more transactions take place via the web.
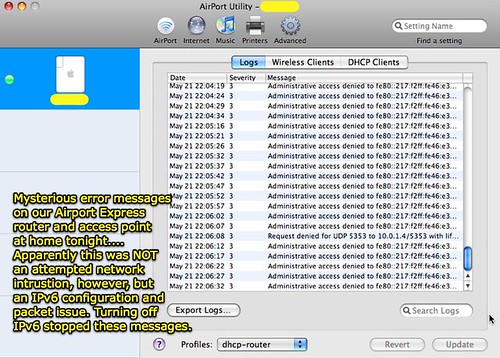
When I saw what appeared to be an unknown device attached to our network, I suspected that a neighbor might have attached his/her computer to our wifi network. To get more information, I accessed the router logs in our Airport Express. I was distressed to see repeated attempts (apparently) to gain administrative access to either the router itself or a computer on our home network:
After I saw this abnormality, I restored the WPA2 password to our router/access point and restarted it. I was very surprised, however, to see the same three MAC addresses of wireless devices again appear in the status window.
As a result, I changed the SSID (network name) of our wifi network and made it a CLOSED network, which means it is hidden from most casual surfers looking for available wireless networks. I also changed the password. After making these changes, the unknown MAC address / wireless computer did NOT successfully reconnect to our network and obtain an IP address, but the mysterious “access denied” messages continued. Several Google searches for the words in the router log turned up this discussion page, which included users suggesting that by turning off the IPv6 configuration in the network system preference (control panel) this error message could be stopped. I turned off IPv6 on my computer, and this mysterious error log message did NOT recur. So…
I’m inclined to think this was a false alarm, in terms of thinking a neighbor had gained access to our home wifi network and was trying to hack into either our router or a computer on our network. It is strange, however, that a device with a different MAC address and its own IP address showed up in our router’s status page. I wish there was a GUI installation for MRTG, or a similar free application which does not require terminal commands to configure with an Airport Express on a network supporting all Mac clients. Router logs need to get MUCH easier to understand and use, IMHO. It’s important for home users to be able to utilize and interpret these, especially when it comes to monitoring the authorized and unauthorized use of a home Internet connection. Unfortunately OpenDNS (which we use at home) does not log information about MAC addresses and IP addresses connected to and utilizing your network. Perhaps this is functionality they could add as additional available statistics.
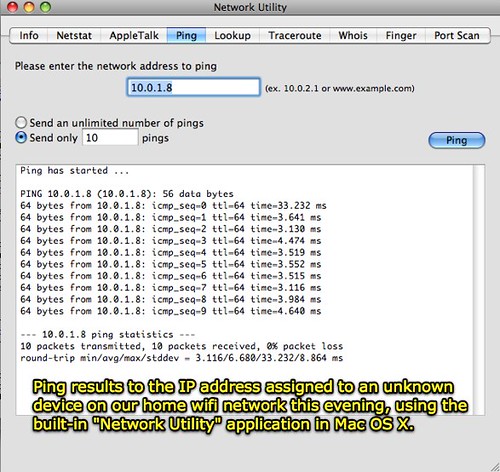
Do you utilize software or hardware tools to monitor access to your home wireless network? If there are simpler and better ways to do this, I’d love to know about them. It is still a mystery to me why a third wireless device was apparently attached to our network this evening. When I “pinged” the mysterious IP address, it returned packets like a “normal” computer would… I think:
Perhaps the IPv6 configuration setting on my computer caused another IP address to be assigned to my Macbook by the DHCP router? I don’t think this was the case, but it would be fairly amazing if one of our neighbors just happened to jump on our wifi network a few hours after I disabled encryption on it for the first time in over a year.
The big relief is that it doesn’t appear someone was trying to “hack” into our network from the outside– these log entries were apparently a result of a misconfiguration or glitch in the router software as it interacts with IPv6 packets.
Technorati Tags:
wifi, wireless, security, home, access, apple, airport, express, mrtg, intrusion
If you enjoyed this post and found it useful, subscribe to Wes’ free newsletter. Check out Wes’ video tutorial library, “Playing with Media.” Information about more ways to learn with Dr. Wesley Fryer are available on wesfryer.com/after.
On this day..
- Communicating with Elected State Representatives via Social Media – 2016
- A Transformed Political Culture in Oklahoma #transformOK #OklaEd – 2016
- Set Your Default YouTube Upload Channel – 2015
- Why Your School Needs a Scratch Club [VIDEO] – 2013
- Help My Son’s Debate Teacher Whose Home Was Destroyed by the Moore Tornado – 2013
- Scratch Camp in Edmond, Oklahoma: June 8-9, 2012 – 2012
- iPad Notetaking: NOT Impressed with PaperPort Notes App – 2012
- Passion Projects, Learning and Innovation – 2011
- Dropped iPad – 2010
- Why Storychasing is relevant for all educators – Contextual learning about copyright is important – 2009

Comments
8 responses to “Neighbors on my WiFi? False Alarm?”
Wesley, there is something you missed in you diagnostic. The private IP assigned by the router/bridge upon wifi connection is normally a DHCP service assignment and the assignment will persist for some time in the DHCP server tables. Changing the SSID and broadcast mode likely required a re-boot of the router/AP which would have purged the table. Otherwise, the IPs assigned by the wireless AP will probably persist for something like 24 hours. Most home routers don’t permit changing that time and the most common I’ve seen is 24 hours.
Is your Wii/Xbox/Playstation still able to connect to the Internet?
Probably not Douglas– and that is a good thought. Since I changed my SSID I’ll need to make the change on my Wii as well…
If you want to add another layer of security, you could also consider turning off DHCP and assigning IP addresses to your machines in one of the private ranges; it’s a bit harder for someone with a wi-fi connection to access your home network that way. You can also use MAC filtering, although of course MAC addresses can be spoofed, too. But it does give you bit more defense-in-depth.
Park outside my house and use my wireless with my blessing. When I pay for hotel net access, I share it with my Airport Express named, “Free Wireless for All.”
I operate under the assumption that the vast majority of people will do the right thing.
If we want kids to have ubiquitous access, communities should remove barriers to home/business router access (IMHO).
My credit card was recently used by someone else for unauthorized purposes and it was IN MY WALLET. A restaurant receipt is a bigger threat to my personal security than someone sniffing packets on my wireless router.
While working with OLPC this week, I used the free open wireless provided by the MIT Media Lab. Not only that, but MIT grants root access to servers upon student request. If they’re not worried, I’m not.
I appreciate your comments on this thread, Gary, as I wrote this I was actually thinking of you because I know you’re an advocate for people sharing their wireless access for the very reasons outlined here.
Just as in the case of Internet safety, I’d like to know if there are actual case studies which support the fears people have. I will follow up with my new OSBI contact to see if this is the case: If people have “gotten in trouble” for sharing their wireless network connection at their house, when neighbors have done illegal things, or if that fear is irrational and not supported by actual case evidence.
I would not be surprised if there are instances where you can get in trouble for allowing others to browse freely on your wireless internet. Primarily because there are ways to monitor internet use and even block network intruders if they are not allowed access to your wireless internet, or if you do not want them searching certain websites.
I’d highly suggest trying this free download of Network Magic, found here: http://www.networkmagic.com/product/internet-monitoring.php
You’ll receive daily email report that include a graph of the Network Traffic for a computer during the previous day. What this graph tells you is how often that computer was accessing your network. This could mean time spent on the Internet (which is most likely the case), time spent accessing a shared file from another computer or time spent printing a document to a shared printer. hope this helps!
Network Magic looks GREAT Derek, I’m eager to try out it. It looks like the free version does not monitor websites visited, but I’m VERY glad they support both Macs and Windows-based systems. It’s unfortunate their current pricing schedule charges more to Mac users than Windows PC users. I am glad Macs are supported tho. I am going to try out this product and will review it here. Mac OS 10.4.7 is required, so this won’t work on my son’s 5 year old Powerbook which is running Mac OS 10.3.9. This definitely looks like a product worth checking out tho…