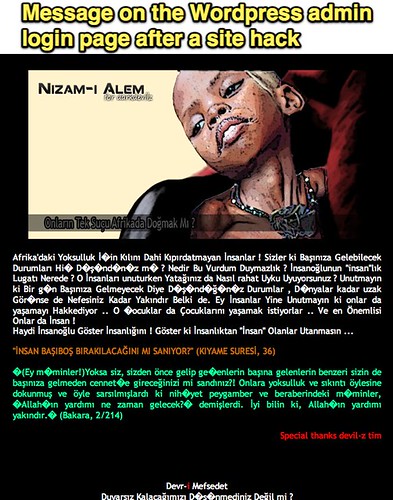
I spent four or five hours today helping a local non-profit group in Oklahoma City get access restored to their WordPress website. The site was hacked by a group apparently from Turkey. They were not able to login to the administrative “dashboard” of their WordPress site. Instead of a login screen, the following message in Turkish was displayed:
Here are the things I think they got WRONG setting up and maintaining their website. Perhaps you can avoid these in a similar situation, and/or encourage others to avoid them.
Inexperienced Developer
The non-profit leaders found someone who literally said “I’ve setup a WordPress site once before” and asked them to setup the site for their organization. This was mistake number one. Just because someone has setup a website with WordPress ONCE, they are neither an expert nor the best choice for your website developer. While their ONE successful WordPress setup may make them an “expert” in WordPress relative to you, if you don’t have any WordPress skills, you still should NOT entrust the future of your organization’s digital footprint to an inexperienced developer. Ask to see a portfolio of work for the websites the person you’re considering as a developer has created, and find out how much they’ve worked with WordPress. This is a challenging thing: Attempting to discern “expert knowledge” when you are not an expert yourself. I’m not aware of formal “WordPress certifications” you can look for on a resume. You definitely don’t want to go with someone who says, “Oh yeah, I’ve done that before one time.”
Setup via Fantastico
Fantastico is a speedy but highly insecure way to setup various content management system installations on a web hosting account, generally using CPanel. CPanel is what most hosting accounts use for management after you login to your web host’s site. While Fantastico can make the process of installing WordPress fast, it also (I’ve read and been told) isn’t as secure as an installation performed from scratch. This takes a bit longer, but from a security perspective is worth it. Ask your web developer, “How are you going to install WordPress on my site? Will you use Fantastico?” If they say yes, ask why. Then go look for a different developer. I know the kid who setup the site which got hacked, and I cleaned up today, used Fantastico for the WordPress installation because I saw the residual files which were left in the web directory by Fantastico. I can’t be sure, but I strongly suspect the INSECURE installation via Fantastico was at least in-part to blame for the hack.
Use a Secure Password
Secure passwords are one of the best defenses against hacks on websites or on web accounts of any flavor. Ideally, secure passwords should also be changed periodically. People don’t like to use secure passwords. These are passwords which are impossible to guess because they use a combination of special keyboard characters along with upper and lowercase letters, AND numbers. No one likes these passwords, but they are the ones we should and must use if we want to keep our sites from being hacked. Don’t use the same password on multiple sites, either.
Keep WordPress Up to Date
Like other software programs, WordPress is regularly “patched” to fix security holes and vulnerabilities. If you don’t update your WordPress installation, you’re vulnerable to hacks. I know for a fact this WordPress installation was out of date. That’s another red flag: If you don’t keep WordPress up to date, you’re asking for trouble and it may come in the form of a hack. Ryan Collins learned this lesson the hard way just this week. Learn from his lessons! Heed the lessons!
Avoid Site Updates on Public Wifi Networks
This final piece of advice is definitely on the conservative side, but it’s relevant since it can open you up to hacks as well. When you use a wifi hotspot at a coffee shop or other location which is not secured, you potentially open yourself up for other people connected to the same network to “sniff” packets being sent from your computer and use the information contained in them to hack your web accounts. The Firesheep extension to FireFox last year dramatically demonstrated this. WordPress installations don’t typically use or require a secure (https://) connection, so cookies which are “set” for site access can be grabbed on a shared public wifi network and used. See my post from November 2010, “Firesheep should get your ATTENTION: Open Public Wifi Dangers are REAL” for additional background. WordPress site access isn’t your only risk: Standard, unsecured FTP connections to your hosting server can also open you up for hacks. Avoid these updates on a public wifi network, or use a VPN “tunneling” service like Astrill to securely and privately use these web applications and programs.
Sometimes your site can be hacked and you may not ever figure out why or how it happened. My site (this blog) was hacked briefly in September 2008. Alan November’s WordPress site (main website) was hacked in July 2010. These things can and do happen. Hopefully, however, we all learn from our mistakes and resolve to avoid “high risk behavior” when it comes to website hacks.
Go forth and behave in secure ways online! (It might save a friend or acquaintance a few hours of work cleaning up the mess made by a bunch of Turkish hackers if you do!)
What pieces of WordPress security advice have I missed here? I’d love to hear additional suggestions on this topic.
Technorati Tags: advice, safety, wordpress, hack, security, installation, cpanel, fantastico


Comments
One response to “A Case Study: How NOT to Set Up a WordPress Site”
After my latest incident, I was almost thinking about just moving to WordPress.com, but decided against it. No real good reason to switch. (And 12 reasons not to… 🙂